143
By
BYOD
BYOD
The practice of an organisations employees using their own computers, smartphones, or other devices for work purposes, rather than the traditional method of the employer supplying all work related devices.
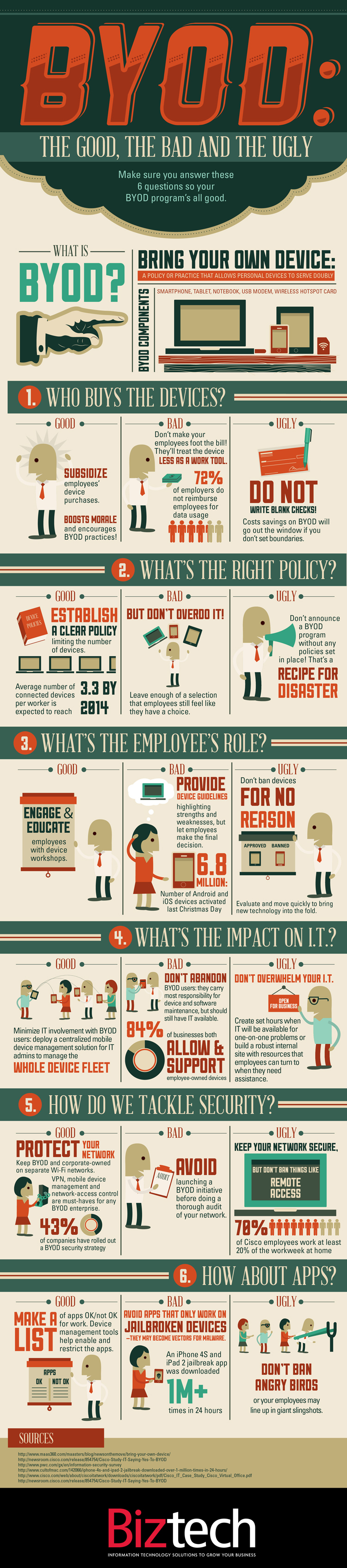
Credit: BYOD: The Good, The Bad, The Ugly | Visually
What is BYOD and why is it important?
These mobile devices are often newer and more advanced than the equipment deployed by many IT departments which are playing catch up and could easily refuse to embrace the BYOD idea. If not fully understood and regulated BYOD can threaten IT security and put a company’s sensitive business systems at risk. Surely it’s simpler to provide approved hardware and software applications so you can retain full control over them?
But Richard Absalom, an analyst at Ovum, believes that BYOD will happen whether a company plans for it or not the best thing that an SMB or enterprise can do is be aware of the benefits and understand the risks.
BYOD benefits and advantages
Key advantages to operating a BYOD strategy:
- increased employee satisfaction (they can work more flexibly)
- cost savings (reduced hardware spend, software licensing and device maintenance)
- productivity gains (employees are happier, more comfortable and often work faster with their own technology).
BYOD risks and disadvantages
While BYOD sounds attractive, businesses need to consider the full implications of allowing corporate data to be accessed on personal devices that they could have little or no control over.
- What data can employees have access to?
- What security measures are in place if an employee’s device is lost, stolen or compromised?
- Increased risk from threats such as hackers and viruses
- Cost to integrate and support a diverse range of employee devices
Planning a BYOD policy
The advent of BYOD is forcing IT departments and IT managers to develop and implement policies that govern the management of unsupported devices. Network security is paramount. Beyond passcode-protecting employee devices, these policies might involve encrypting sensitive data, preventing local storage of corporate documents and/or limiting corporate access to non-sensitive areas.
Credit: The full and original article was published on Tech Radar
Thanks for stopping by!
Discovered, created or written something great that links to this element? Share links, articles, videos podcasts or infographics here.
Fill in your details and tick which resource you'd like to share.